Scoped Enclave vs. Full Enterprise: How to Right-Size Your CMMC Compliance
- clairekelley0
- Apr 7
- 3 min read
Under Phase 1, CMMC compliance has become a condition of contract award. DIB contractors are now seeing CMMC requirements appear in new solicitations. Success in CMMC 2.0 is about right sizing your environment during the discovery and scoping phases before an assessor ever sets eyes on your CMMC implementation.
To define an accurate assessment boundary, you must first track the flow of Controlled Unclassified Information (CUI) through your organization. Starting with how you receive it from your clients, which functions need to use it, where it is processed, how it is stored, if you send it to your suppliers/partners, and how it eventually flows out or is destroyed.

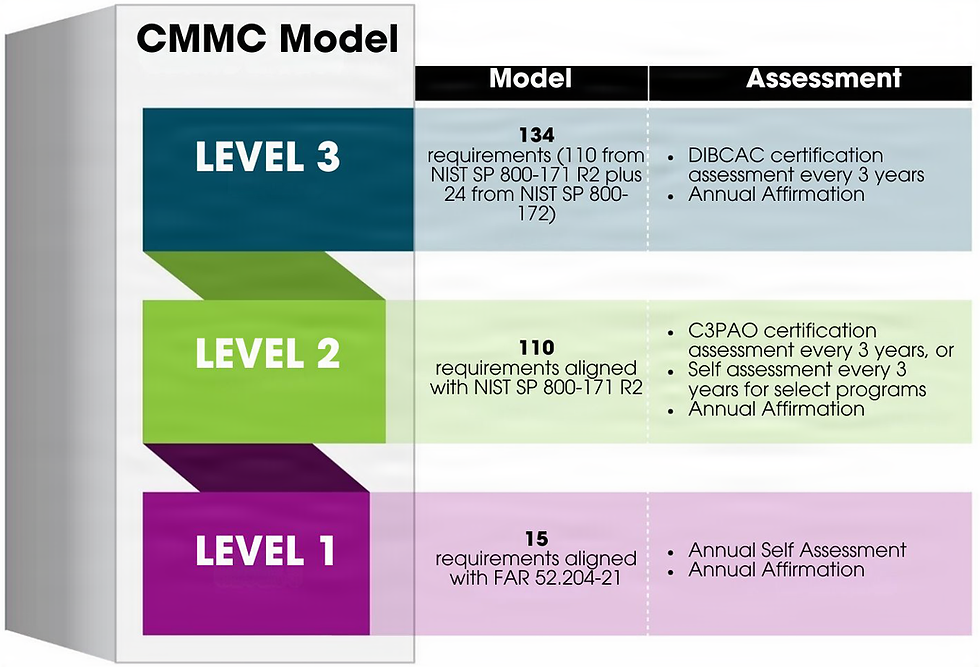
Right-sizing your scope is a financial imperative, not just an IT task. Organizations that fail to map data flows often default to over-scoping, bringing their entire corporate network under the scrutiny of an assessor. This could lead to massive, unnecessary costs in applying all 110 NIST SP 800-171 controls to devices and users that never even touch CUI. "Understanding which data to protect, how it flows in, is stored, used, and flows out is critical to right-sizing your cybersecurity plan." said Joe Devine of AXIOTROP.
CMMC compliance is not limited to digital files. You must account for CUI in every format it takes.
• Digital Security: This includes encrypted servers, Virtual Desktop Infrastructure (VDI), and ensuring that any Cloud Service Provider (CSP) utilized meets FedRAMP Moderate (or higher) standards.
• Physical Security: This requires secure storage for paper media, locked file cabinets for sensitive diagrams, and restricted access to physical workstations.
To minimize your assessment scope, you must move beyond broad, IT-level permissions and focus on reducing the internal need to know personnel and systems that will “see” CUI. By conducting specific departmental and individual access reviews, you align with the Personnel Security (PS) and Access Control (AC) domains. This directly reduces the volume of background checks, training records, and monitoring logs an auditor must review, effectively accelerating your path to certification.
By isolating CUI within a dedicated environment, you can draw a strict boundary around specific systems and people. This limits the CCA’s (CMMC Certified Assessor) scrutiny to a small, hardened environment rather than your entire network/facility. Reducing your CUI footprint is also the fastest way to increase your SPRS score.
For small and medium-sized businesses (SMBs), practical scoping will help in managing the high costs and legal risks associated with CMMC compliance. To remain competitive without over-engineering in their systems, SMBs are encouraged to use Governance, Risk, and Compliance (GRC) tools and external partners like CMMC Third Party Assessor Organizations (C3PAOs) or Registered Provider Organizations (RPOs). These CMMC specialists can provide a structured roadmap and executive-level visibility, helping to avoid unnecessary costs that stem from improper initial scoping.
As we move through the Phase 1 rollout, CMMC requirements have started to appear in DoW contracts as early as Q1 of 2026. This includes DFARS 252.204.7021 CMMC Level 2 with 3rd Party assessment required. As we approach November 10th of 2026, it is important to start your CMMC journey before your contract requires it!
About AXIOTROP, LLC:
Ready to start your CMMC journey? Begin by identifying your cybersecurity gaps and building a tailored remediation plan and budget. AXIOTROP’s mission is to make cybersecurity accessible, attainable, and sustainable for small and medium-sized businesses, so they remain competitive and poised for growth. We simplify cybersecurity by working closely with businesses to right-size their program for their needs, resulting in client retention, business expansion, and reduced risk.



Comments