CMMC Cybersecurity Documentation Guide
- clairekelley0
- Mar 31
- 2 min read
Complying with CMMC requirements means strong documentation. Some companies choose to put all their documentation in a single System Security Plan (SSP) to reduce the number of controlled documents. However, we recommend a layered documentation approach to segment the security plan and to ensure the needed information gets to the right people.

This documentation approach is built upon four layers: a high-level narrative of the security strategy, security policies, detailed control implementations, and a commitment matrix to track responsibilities. Strong documentation ensures alignment with NIST SP 800-171 and CMMC compliance.
Level 1: Security Strategy
This serves as the "reader-facing" component of your security documentation suitable for clients, suppliers, employees, and other partners. It provides a high-level narrative of your security initiatives, detailing:
Which security domains make up your security program.
Sensitive data flows and system security management.
Information/data classifications you consider important.
Security roles and responsibilities.
Security governance.
Protocols for monitoring and testing.
Level 2: Security Policies
While the narrative provides context, security policies dictate the "we-shall" of the security program.
Separate policy documents covering your implemented cybersecurity domains, define the policy statements that cover your control implementations designed to secure information and meet compliance requirements.
These policy statements do not define the technical implementations that provide coverage of the "we-shall" statements. This allows the organization to change technical implementations without updating policies.
Level 3: The System Security Plan (SSP)
The SSP represents the operational backbone of your security program. This large document is typically more than 100 pages and documents the actual security control implementation details.
These control implementation statements provide a complete description of the policy and technical implementations of each required security control.
The SSP needs to reference all relevant policies, procedures, and other documents that provide context for the control implementations.
All assessment objectives must be described for each security control.
Level 4: Commitment Matrix
The commitment matrix is the differentiator that prevents your SSP from becoming "shelfware."
The matrix serves as a tactical blueprint for tasks, responsibilities, and timelines.
It ensures continuous adherence to internal policies and regulatory requirements, transforming documentation into an active commitment to security.
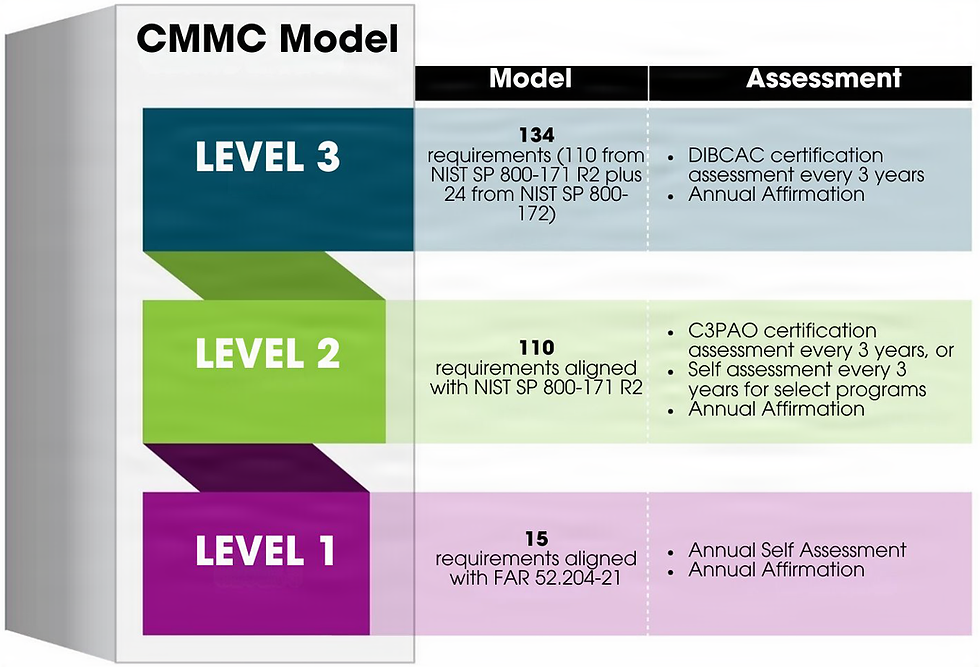
Achieving CMMC is more than a regulatory hurdle; it is a demonstration of your organization’s role in the integrity of the national defense supply chain. Is your organization prepared for the CMMC Phase 1 checkpoints, or is your documentation still a work in progress? Establish your four-level security documentation today to ensure you are eligible for the DIB contracts of tomorrow.
About AXIOTROP, LLC:
Ready to start your CMMC journey? Already down the CMMC path and need assessment support? Either way, AXIOTROP should be your next call.
AXIOTROP’s mission is to make cybersecurity accessible, attainable, and sustainable for small and medium-sized businesses, so they remain competitive and poised for growth. We simplify cybersecurity by working closely with businesses to right-size their program for their needs, resulting in client retention, business expansion, and reduced risk.



Comments